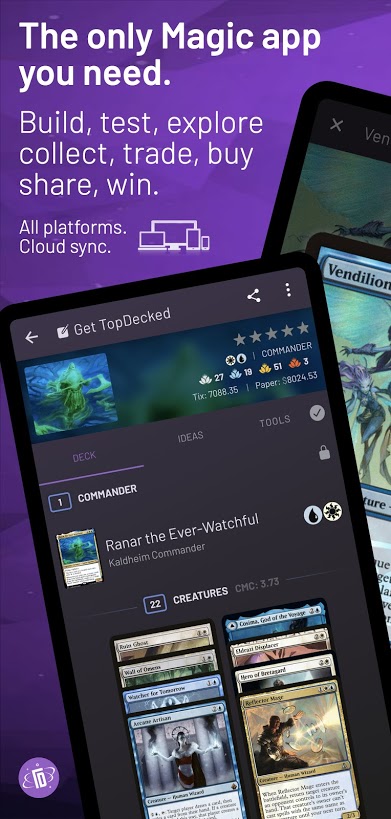
While migrating an e-commerce application (piqchocolates.com) from Grails and Tomcat to an AngularJS, Java EE (JAX-RS), and JBoss WildFly stack, I had to make sure that the new platform has feature parity in all areas that are valuable to our business. Search Engine Optimization (SEO) is crucial for us because we primarily market our business on-line. In short, we need search engine optimized URLs, and deep linking; this article will show you how to implement both.
rvm command, a very simple and intuitive “Ruby Version Manager”:
mkdir -p ~/.rvm/src && cd ~/.rvm/src && rm -rf ./rvm && \ git clone --depth 1 git://github.com/wayneeseguin/rvm.git && \ cd rvm && ./install && \ echo "if [[ -s $HOME/.rvm/scripts/rvm ]]; then source $HOME/.rvm/scripts/rvm; fi" >> ~/.bashrc
\curl -L https://get.rvm.io | bash
rvm install 1.9.3

I’d like to take a brief moment to let everyone know that we’re going on a Conference Tour! I’ll be presenting on [[Rewrite]] at South-east Linux Fest (FREE) in Charlotte, North Carolina at the Blake Hotel (June 7-9).
I’ll also be presenting [[Rewrite]], Errai, and JBoss Forge at JUDCon Boston 2013 (June 9-11):
So please come join me for a fun and hopefully informative few sessions!

If you have ever used Google Calendar, Siri, Android Voice Command or other natural language tools, you might be familiar with convenient calendar features and voice calendar control. 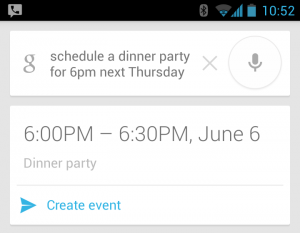 “Schedule a dinner party for six pm, next Thursday,” and The start time for your dinner party conveniently shows up, ready for your finishing touch. But how does this work? Can we use it for our own applications?
“Schedule a dinner party for six pm, next Thursday,” and The start time for your dinner party conveniently shows up, ready for your finishing touch. But how does this work? Can we use it for our own applications?
If you’ve given this a bit of thought, you’ve probably figured out that in order to understand grammar, the nearly infinite possible combinations of words, expressions, numbers, and dialects should require a not insignificant amount of computing power, and a good deal of creativity.
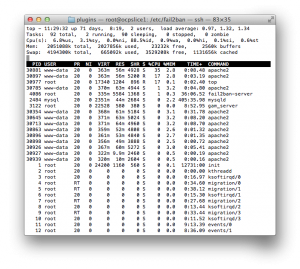
Frequently spammers target products such as wordpress, web forum software, phpMyAdmin, and other common tools used by hobbyist and professional website administrators.
Whether you are hosting your own blog, or running a website for your company or more, it can be difficult to deal with the increasing amount of malicious web traffic seen on a daily basis, while still allowing friendly crawlers such as Google, Yahoo, and MSN search engines.
This harmful and wasteful traffic may damage your system or simply waste its resources, slowing down the site for your more welcome users. If this sounds familiar to you, but your page hits don’t seem to add up, then you may want to consider taking some of the measures outlined below in order to secure your site from harmful hacks and sluggish spam.

For all of you who are trying to figure out how to integrate with Google’s single sign-on functionality, this article might be for you. I’ve taken the liberty of condensing all of the actual logic required to perform OAuth Google login, and provided it as a class and a JSP (seen below). In order to follow along better, I suggest cloning the example GitHub repository, and deploying to the application to your server of choice.

 Craig Schwarzwald
Craig Schwarzwald